You can add custom tools by creating new modules under mcp_server/tools/ with the @tool decorator and registering them in server.py. All tools—search engines, APIs, and automations—are simply different MCP implementations that you can freely add, remove, or replace.
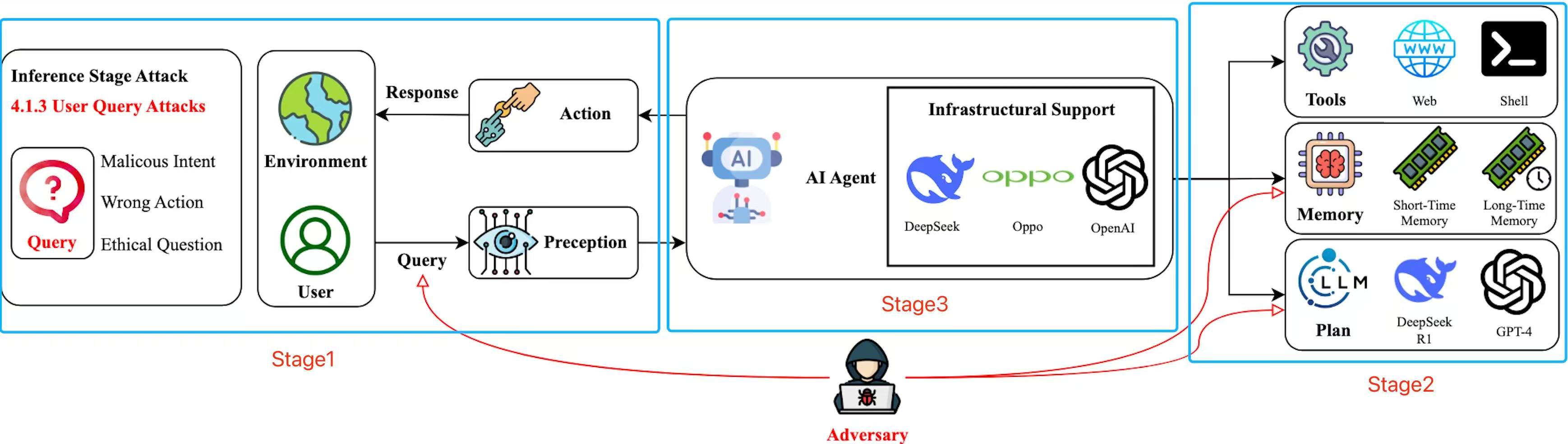
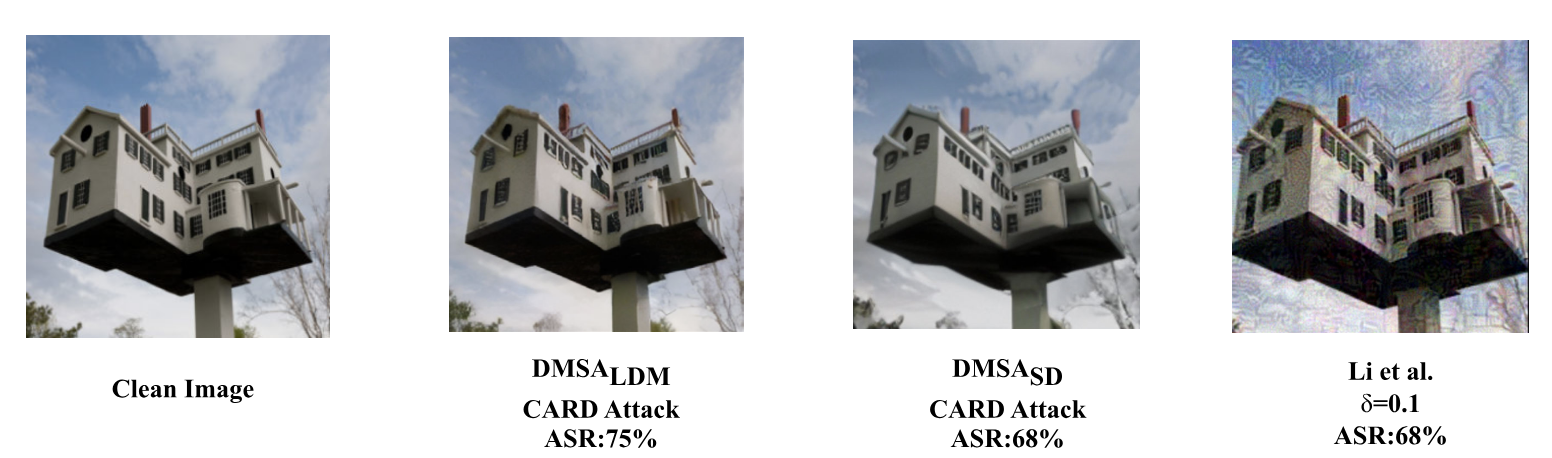
Figure 1. Current AI agent systems suffer from various adversarial attacks and generate harmful or illegal responses.
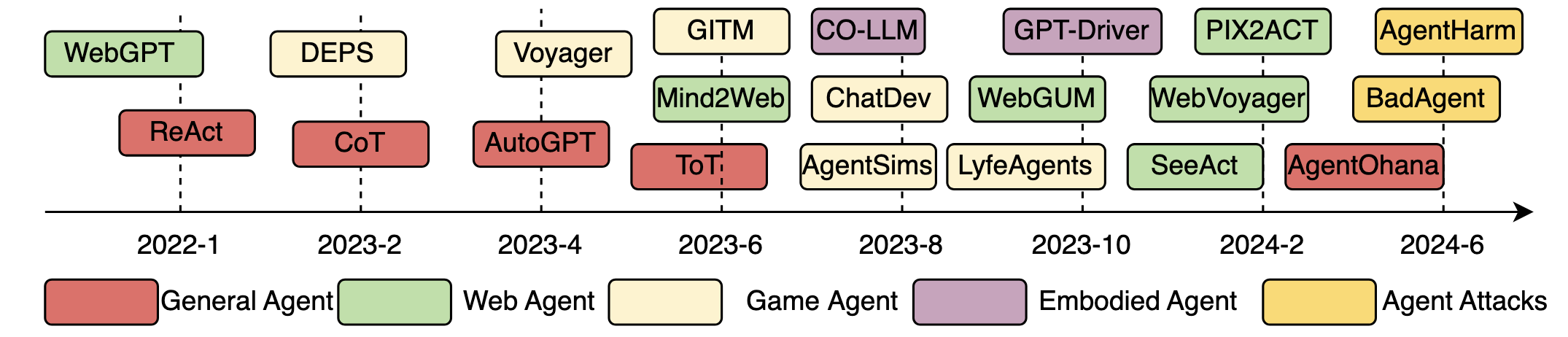
Figure 2. Major events related to AI agents and its security.
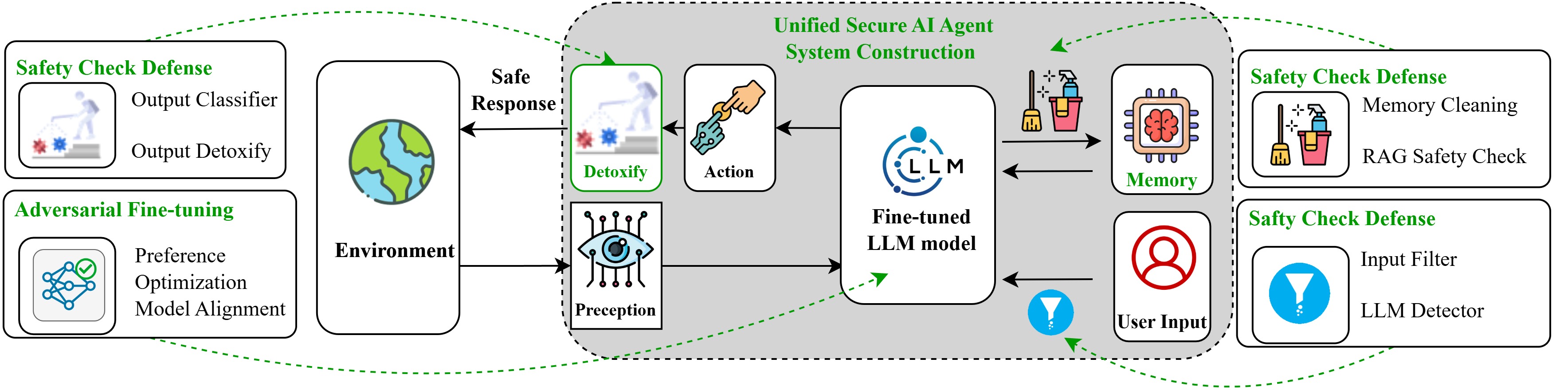
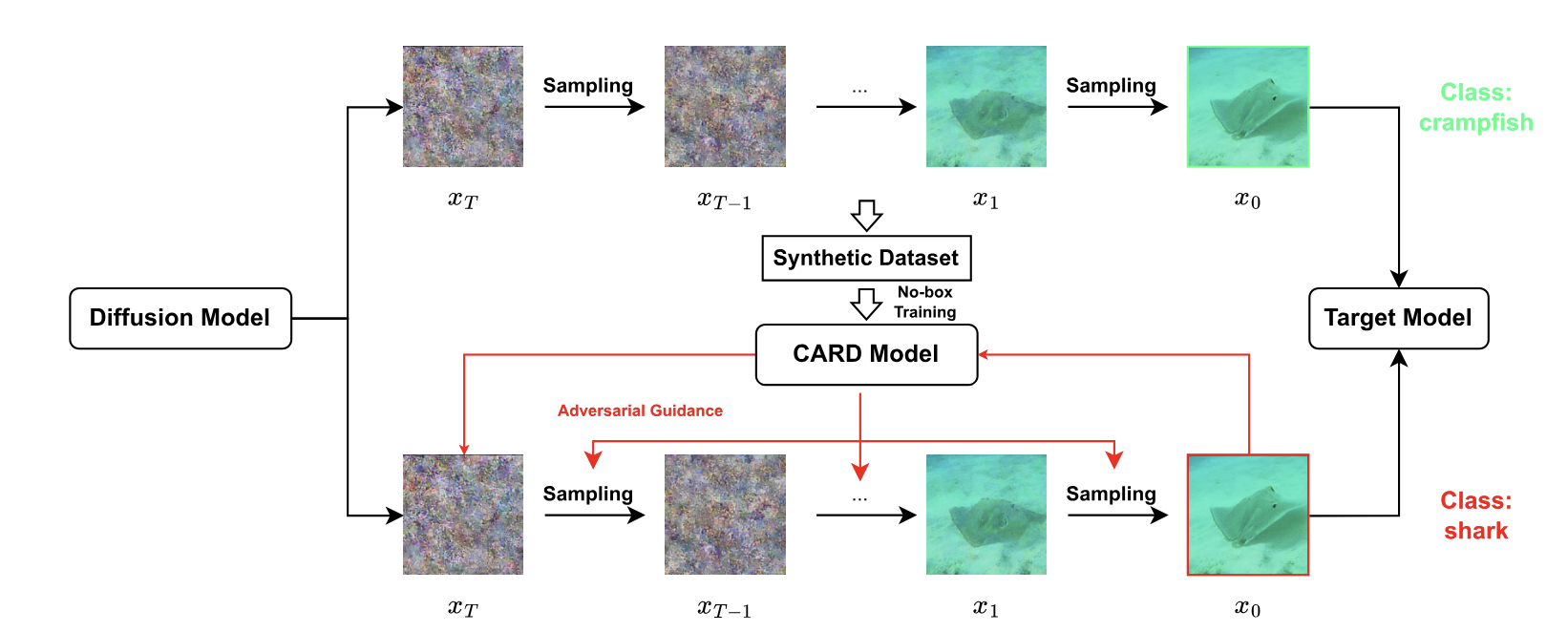
Figure 3. An overview of the proposed secure AI agent system framework.